CompTIA CySA+ CS0-002 Study Guide is new updated. PassQuestion can provide a shortcut for you and save you a lot of time and effort. PassQuestion will provide good CompTIA CySA+ CS0-002 Study Guide for your CompTIA CySA+ certification CS0-002 exam and help you pass CompTIA Cybersecurity Analyst (CySA+) Certification CS0-002 Exam successfully in your first time.
The CompTIA Cybersecurity Analyst (CySA+) certification verifies that successful candidates have the knowledge and skills required to leverage intelligence and threat detection techniques, analyze and interpret data, identify and address vulnerabilities, suggest preventative measures, and effectively respond to and recover from incidents.
Exam Details
Required exam: CS0-002
Number of questions: Minimum of 85
Type of questions: Multiple choice and performance-based
Length of test: 165 minutes
Recommended experience • 4 years of hands-on experience in a technical cybersecurity job role
• Security+ and Network+, or equivalent knowledge and experience
Passing score: 750 (on a scale of 100-900)
Price: $359 USD
CompTIA CySA+ CS0-002 Exam Topics
The table below lists the domains measured by this examination and the extent to which they are represented.
1.0 Threat and Vulnerability Management 22%
2.0 Software and Systems Security 18%
3.0 Security Operations and Monitoring 25%
4.0 Incident Response 22%
5.0 Compliance and Assessment 13%
View Online CompTIA Cybersecurity Analyst (CySA+) Certification CS0-002 Free Questions
1.An analyst is performing penetration testing and vulnerability assessment activities against a new vehicle automation platform.
Which of the following is MOST likely an attack vector that is being utilized as part of the testing and assessment?
A. FaaS
B. RTOS
C. SoC
D. GPS
E. CAN bus
Answer: B
2.An information security analyst observes anomalous behavior on the SCADA devices in a power plant. This behavior results in the industrial generators overheating and destabilizing the power supply.
Which of the following would BEST identify potential indicators of compromise?
A. Use Burp Suite to capture packets to the SCADA device's IP.
B. Use tcpdump to capture packets from the SCADA device IP.
C. Use Wireshark to capture packets between SCADA devices and the management system.
D. Use Nmap to capture packets from the management system to the SCADA devices.
Answer: C
3.Which of the following would MOST likely be included in the incident response procedure after a security breach of customer PII?
A. Human resources
B. Public relations
C. Marketing
D. Internal network operations center
Answer: B
4.An analyst is working with a network engineer to resolve a vulnerability that was found in a piece of legacy hardware, which is critical to the operation of the organization's production line. The legacy hardware does not have third-party support, and the OEM manufacturer of the controller is no longer in operation. The analyst documents the activities and verifies these actions prevent remote exploitation of the vulnerability.
Which of the following would be the MOST appropriate to remediate the controller?
A. Segment the network to constrain access to administrative interfaces.
B. Replace the equipment that has third-party support.
C. Remove the legacy hardware from the network.
D. Install an IDS on the network between the switch and the legacy equipment.
Answer: D
5.A small electronics company decides to use a contractor to assist with the development of a new FPGA-based device. Several of the development phases will occur off-site at the contractor's labs.
Which of the following is the main concern a security analyst should have with this arrangement?
A. Making multiple trips between development sites increases the chance of physical damage to the FPGAs.
B. Moving the FPGAs between development sites will lessen the time that is available for security testing.
C. Development phases occurring at multiple sites may produce change management issues.
D. FPGA applications are easily cloned, increasing the possibility of intellectual property theft.
Answer: D
6.A security analyst is trying to determine if a host is active on a network.
The analyst first attempts the following:
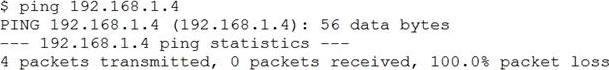
The analyst runs the following command next:
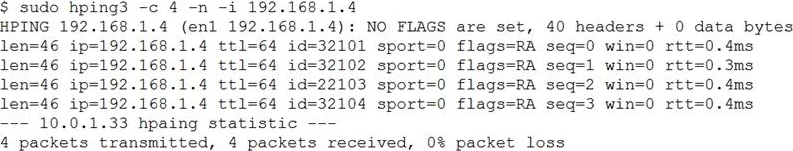
Which of the following would explain the difference in results?
A. ICMP is being blocked by a firewall.
B. The routing tables for ping and hping3 were different.
C. The original ping command needed root permission to execute.
D. hping3is returning a false positive.
Answer: A

No comments yet