How To Protect Your Smart Home
As technology becomes more and more prevalent inside our homes; everything from speakers, to TVs, to washing machines, fridges, light bulbs, doorbells, thermostats, and even fish tanks are being connected to the internet. This comes with some risk. Hackers can now break into your home without ever setting food in it. In this article, I'm going to give you some tips on how to protect yourself and your family.
This article is the third in a series of how to protect yourself from hackers. The first two cover protecting your online accounts and your devices from hackers, respectively; so don't forget to check those out as well.
First up, let me say that I love technology and I have quite a few networked gadgets all around my home. The thing is... I've been working with technology for a long time. I'm used to evaluating products, assessing their security, and designing a safe topology within which they can be deployed. Companies... some companies take a lot of care to ensure they are not compromising the security of their systems when they do this; and will bring in outside expertise to make sure they get it right. You can't expect the same sort of rigor to be applied by the general public.
Who goes to the shop to buy a washing machine, and has a security consultant come and perform an assessment of it's networked services? This sort of thing catches companies out all the time. There's an American casino that got hacked because of an internet-connected fish tank in its lobby.
The buzzword for this growing collection of devices that hook themselves up the internet is called the "internet of things" or IoT for short. If it can catch a casino with a dedicated security team flat-footed, your average consumer at home is definitely at a disadvantage.
It doesn't help that a lot of the time this internet connectivity is included as an afterthought. Washing machines aren't getting designed around their network connectivity. They're designed primarily around their ability to wash clothes, and then other factors like energy efficiency and noise. So you've got a decent design for your washing machine and then you find out your competitor's has an app.
Marketing say you need an app too. Right... what's the cheapest thing we can buy to stick in there and make it internet-connected so we can have an app too? As you may have guessed, the cheapest thing is not usually the most secure thing . There are a lot of devices on the market with really cheap and nasty connectivity. That leaves you exposed.
There are some horrible stories floating around of people being watched in their own homes, through their own cameras, by strangers on the internet. Of people coming into their child's bedroom to overhear some creep talking to them through the baby monitor. There are stories of people having their thermostats messed with - cranking up or cutting off the heat in the baby's room.
If your internet-connected fridge is set to holiday mode or your thermostat is set to away mode, a burglar could know when it's safe to break in... if they need to break in at all. If you've got a smart lock and it gets compromised, they may as well have a key. If just one of these devices gets compromised, it can be used to attack everything else on your home network.
My goal here isn't to scare you. More to get you to think about the devices you've got on your home network, and what risk they might pose. This isn't a joke, and it's not the case you'll be saved by anonymity. There is literally a search engine that anyone can use that scans the internet for insecure devices. You can use it to search for vulnerable devices in people's homes and it will tell you what they are, where they are, and how to access them. It's that easy. So what can we do?
Reputation & Account Security
First of all, do a bit of research on the company who made the product. If you Google your internet connected products, do a whole host of horror stories come up? That might be a good sign not to buy it. Now I should point out that just because a few people got hacked doesn't mean there's something wrong with the product itself. A lot of the time the device is fine but the person who got hacked was using a terrible password, and it was there account that got compromised.
Default Passwords
It does lead me onto the topic of default passwords, though. When you get a new device; always, always change the default password. Some devices these days come with a random password instead of the same password for every customer. Change it anyway. Some of these are not as random as they seem. In some cases there are only a handful of different passwords, and they just cycle through them. In others, those random looking letters and numbers are actually the device's physical MAC address (not to be confused with an Apple Mac). The problem with using the MAC address is that's how other devices in the network connect to it, so it can't be a secret - it's actively advertised. In the case of a wireless router, it is blasting that MAC address across the airwaves for anyone to see. Change the password!
If you don't change the password, it's like leaving your front door open with a sign saying "please don't rob me". When one of those scanners find your device on the internet, you can guarantee the first thing they're going to do is try and log in with the default password. This isn't just for home users.
In years gone by I used to onboard a lot of new customers for our support team at work. There were always devices on the network that weren't documented, and more often than not I was able to get into them just by trying a few default passwords. Printers are a big culprit in the corporate world.
Firmware Updates
The next thing you should do with any network-connected device is check for software or firmware updates. Anything with network connectivity should receive updates. No software is ever perfect, and as flaws are discovered that can be exploited, the vendor should be providing updates to fix them. On your computer or your phone, the updates are probably pushed to you; so you don't have to do much other than agree to them.
For a lot of IoT devices, though, this isn't the case; so you have to remember to check yourself and install any updates, manually. This is a good thing to check before you buy. How does a device get updated? If it's automatic, great! You're good. If it's a manual process then plan to be in the habit of checking and applying them. If there is no way for it to receive updates, don't buy it! That's a sure sign they've shoehorned in the cheapest bit of connectivity they could find, and didn't bother to think about security at all. This is important.
A quick search for camera I own shows 35 different vulnerabilities that have been reported that affect it, specifically. Fortunately, my device has been updated to protect against them; but only because i went to the manufacturer's website, downloaded the new firmware, and installed it on my camera. Otherwise that would be 35 different ways to try and break into my home.
Features you don't need
Speaking of my camera, here's another tip. If you don't need internet connectivity, turn it off. The camera I'm talking about is used as a baby monitor. It has an internet-connected feature that lets me check my baby from anywhere in the world. That's... not a feature I'm ever going to use. The way I see it, if I'm in a position of needing to use the internet connectivity, I'm not in a position to be able to comfort my child anyway, so what's the point? If that's enabled, it's open for anyone in the world to try and abuse it. So because I don't use that feature, I've turned its internet connectivity off. I don't need that to use it in my own home.
So take a look at your devices, and the features they offer. Turning off every feature you don't actually use can dramatically reduce the attack surface of your home.
Wireless Security
The heart of most home networks is of course your router. Technically speaking, it's probably a combined router, switch, firewall, wireless access point, and modem; but we'll stick with the name "router". Hopefully you've taken my earlier advice, and you've already changed both its administrative password and the password for the wireless network. There's more to it than just the password itself, though. Most routers come with various levels of security that can be enabled.
Unfortunately for most home readers, the default setting is to enable all of them. This is simply because a lot of home users would get confused if asked to choose their own settings, so the router makers just switch everything on to make it as easy as possible for people to get up and running. The downside of course is that by enabling options with weak security, you also make it easier for hackers to get in, too.
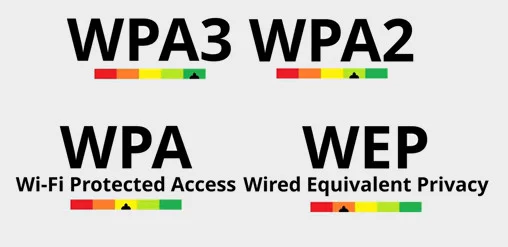
The most likely options you'll have for wireless security are WEP, WAP, and WAP2. The latest devices may also support WPA3. There are variations on these including personal and enterprise versions. For most home users you'll be after the personal version that uses a pre-shared key. Enterprise versions are aimed at businesses and are more secure, but require more knowledge and infrastructure to set up.
The general rule to follow is that you want to start with the most secure, work your way down, and only enable the security options that are absolutely necessary to allow your devices to connect.
WAP3 is the latest and greatest so if you have that, turn it on. A lot of devices at this time are not going to support it, so you'll almost certainly want to enable WPA2 as well. For the time being at least. In most cases you won't need to enable vanilla WAP. WPA2 has been around for 16 years, so it's pretty well supported. If in doubt, keep WAP1 turned off and see if everything works. If it doesn't, try reconnecting the device to the network. If it still can't connect then try it with WAP enabled. The same logic applies to WEP, although that's so easy to breach these days you really want to avoid using that if at all possible.
Another problem with home routers is that most come with a feature called WPS enabled. That stands for Wi-Fi Protected Setup, and it lets you connect to your network without knowing the password. It was designed to make it easier for people to connect to their own network, but of course making it easier for home users means making it easier for hackers as well. WPS can work either by pressing a button on the router, or by entering a PIN code.
When you press the button your network is vulnerable for a short time, when basically anything can now connect without knowing the password. This isn't too bad because an attacker would have to be in range and try to connect at just the right time.
The PIN code method is basically a terrible idea that makes your password pointless, as it's far too easy to brute force the PIN and crack it, instead. According to the WPS standard, the button is optional and the PIN code is mandatory. So if your router supports WPS (which most do), the really insecure PIN option is most likely turned on. Disabling WSP altogether is the best approach, although some routers will allow you to disregard the specification and disable the PIN whilst keeping the button enabled; which could be a reasonable compromise.
Firewall Hardening
If you think I'm done having to go at home routers, think again; because there are another couple of common security mistakes worth talking about. As mentioned, a typical home router is also a firewall. A firewall's job is to prevent outside connections unless you explicitly say they're OK. Sometimes this means you'll need to tell the firewall to allow a particular type of connection in order to get a device working.
In a business, this list of access rules is usually pretty tightly controlled by someone who understands networking; but home routers are designed to be operated by people who don't understand this stuff, and so they make a few compromises in the name of ease of use.
One of these compromises is their DMZ feature. In a business setting, a DMZ network is used as a security boundary, and it's a good thing. In home routers, the DMZ function usually means you get to pick a DMZ device, and it basically turns off all protection for it. Any random connections from the internet now get forwarded straight to that device without any filtering at all, exposing every piece of connectivity that device has to anyone on the internet.
Whilst this will work around any firewall issues you might be having with that device, it's about the worst possible thing you could do from a security perspective. So my advice here is simple. If your home router has a DMZ feature, don't use it. Ever. It's bad. It's really bad! Find out what access rules the device needs and configure them. Like I said, in a business network a DMZ means something different, and it's not a simple button you can click to make your Xbox work. At home, it probably is, and you should probably never click it.
The other feature home routers get that can compromise your security is c, or Universal Plug and Play. This is a much better solution than the DMZ feature, but it still has its issues. Remember that list of access rules? Well, the UPnP protocol allow a network devices to instruct the firewall which traffic to allow through. The access rules are then added automatically. This is actually really handy in a home network, because it means your devices can enable just the right amount of connectivity they need rather than completely disabling the firewall like a DMZ does; and it all happens without the need to have a network consultant on hand.
The problem is you don't know what exactly has been allowed into your network with UPnP enabled. Business routers simply don't have this feature, because access needs to be checked and approved. The ability for random devices to make arbitrary changes to network security without any review just wouldn't fly in a business.
Let's go back to my camera. Let's say I can't find a way to switch off remote access. In a business network it wouldn't work anyway, unless the network team allowed it. At home it might have used UPnP to open up ports in your firewall. If I disable UPnP I can gain more control and choose to allow or disallow that access on my firewall.
A lot of people would argue that UPnP is a terrible feature, and you should turn it off. I wouldn't go that far. Certainly it has no place in a business network; but at home it's a pragmatic solution the majority of the time, and if you disable it some things may stop working. What I would recommend doing is at least taking a look at what access it has opened up when you add a new device for new features. If it looks sensible, you could leave it as-is; or you might choose to disable it and configure the firewall rules yourself. If it looks like it's opening up too much access, then taking manual control becomes the obvious choice. If you're a more advanced user you may well choose to throw away or at least supplement your home router's built-in firewall with something a bit more robust.
This is definitely the most secure of the options. It will remove weaknesses like UPnP and give you the ability to create a real DMZ if you wanted. It also gives you control over vulnerabilities in the firewall itself. Sometimes that box you get from your internet provider can be full of security holes itself; because just like with cheap internet of things devices, your ISP couldn't be bothered providing timely updates to resolve vulnerabilities that were discovered in whatever third-party device they've slapped their logo on. You may even go as far as separating your smart devices into a different network from your other devices.
There are a lot of options here, but we're getting into the territory of designing an enterprise network in your home; and I need to bring this article to a close. Let me know if you found this useful.