Microsoft Advanced Threat Protection (ATP) Explained
Microsoft's Advanced Threat Protection technologies are designed to provide you with cutting-edge cyber defences. So when people ask me whether they should buy Advanced Threat Protection, I always say... Er which are you talking about? Because there are three different Microsoft products with the name Advanced Threat Protection, and that can be confusing. So this article is going to introduce all of them.
I'm covering three different solutions here, so this article is going to be more of an overview rather than a deep dive. If you want me to cover a particular Advanced Threat Protection solution in more depth, then drop it in the comments below.
The current three Microsoft Advanced Threat Protection solutions are:
- Microsoft Defender Advanced Threat Protection
- Azure Advanced Threat Protection
- Office 365 Advanced Threat Protection
Although the way they've been renaming things recently, there's every chance that last one will end up as "Microsoft 365 Advanced Threat Protection" at some point in the future.
To save myself some time, I'm probably going to abbreviate the phrase "Advanced Threat Protection" to "ATP". There is some linking between these solutions, but they can largely be considered as standalone products.
Microsoft Defender ATP (Microsoft Defender for Endpoint)
If you're thinking the name "Microsoft Defender" sounds familiar, that's because it's also the current name of the antivirus and firewall features built into Windows 10 and Windows Server. That probably gives you an indication of where this solution is focused. Primarily, it's for your endpoints. Defender ATP isn't an upgraded antivirus, though. It's more like an analytics tool that lives in the cloud, but it is deeply woven into the Windows operating system and receives telemetry from Windows Defender antivirus, amongst other things.
Every copy of Windows 10 or recent server versions has a built-in Defender ATP service that lies dormant, but once activated with the right license will monitor activity on the device and feed data up to the Microsoft cloud.
With Windows this is baked into the operating system itself; although there are agents you can install on Mac and Linux as well. Once enabled, this basically sucks up a load of data from your devices, combines it with Microsoft's global telemetry, crunches it up with machine learning, and gives you access to a ton of information about the security stance of your endpoints.
Don't let the "Defender" name fool you - this is about more than antivirus. I mean yes, it will tell you about the antivirus state and any detections if you're using Microsoft Defender as your antivirus, but does a whole lot more as well. It has the sort of data you'd expect - malware detections, suspicious activity, audit information like device and software inventories... but it's what it does with this information that's most interesting.
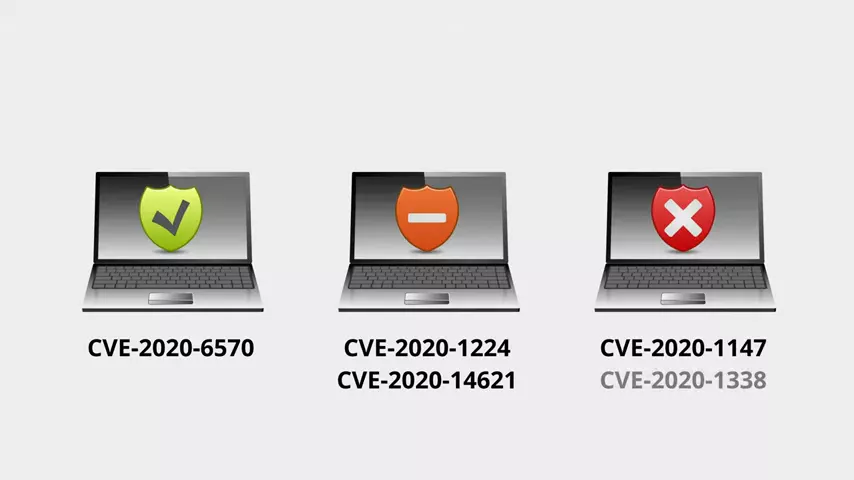
You can look at the risk state of each device, what CVEs it's vulnerable to, what you need to patch to fix it, etc., etc.;
but even more interesting Microsoft use their global telemetry to proactively identify where you're most exposed. Let's say there's some nasty ransomware doing the rounds. Microsoft can see this through their global telemetry, and flag it through the security portal.
They can use the information collected from your endpoints to not only detect if you've been affected by it, but also what devices might be particularly vulnerable to compromise, and provide you with recommendations to mitigate the risk. This might be to patch a particular piece of software, or apply a particular configuration change. You can even get an analyst's report explaining the threat in detail, which is pretty cool.
Defender ATP can also be used to trace an attack post-breach using its threat hunting capabilities to analyze the data it has collected. Some of this can even be automated, with automatic investigations and remediation actions doing a lot of the grunt work to piece together a picture of events using related data, and allowing your security analyst to go get a coffee instead.
Azure Advanced Threat Protection (Microsoft Defender for Identity)
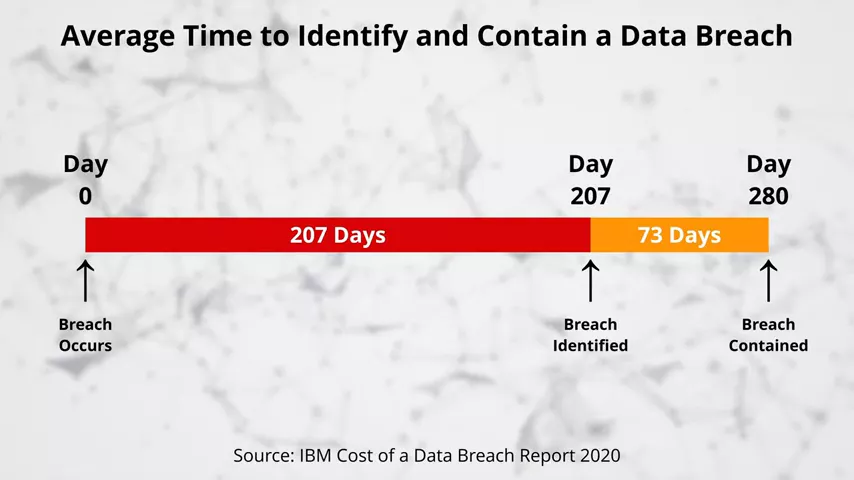
Azure ATP is all about reducing the time it takes to detect a breach. That's "detect", not "prevent"; because no defense is perfect and if all your effort is focused on prevention, then when something does slip past you're in a lot of trouble. Te stats in this are pretty bad. On average once an organisation is breached, it takes more than six months for them to realise.
In that time an attacker can gain access to a lot of data, they can steal a lot of data, and they can set themselves up to do a lot of damage.
Azure ATP tries to reduce that breach window right down. Unlike Defender ATP, Azure ATP doesn't care about what software is doing on your device. Instead, Azure ATP looks at you and your behavior.
The theory goes like this: technology will always have flaws that can be exploited. You can beat the tech, you can steal someone's credentials, you can get into the network; but what an attacker can't do is accurately replicate someone else's behavior. So Azure ATP analyses user behavior on the network - the devices they use, and the resources they access in a normal day; and it builds up a behavioral profile for that user. If an attacker manages to breach that user's account and use it to access the network, they don't have to do anything specifically dodgy to trip the alarm. Azure ATP will simply determine that the user is behaving in a manner that is uncharacteristic for that individual, and will flag it as anomalous behavior.
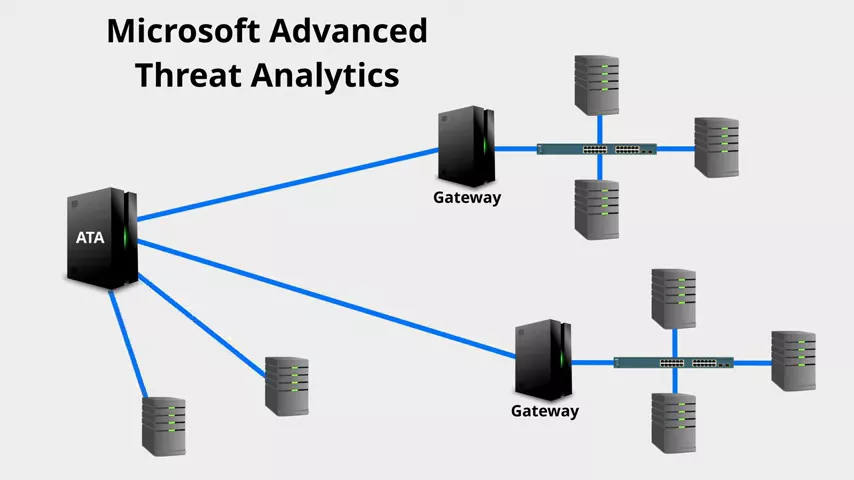
Azure Advanced Threat Protection is essentially the semi-cloud-based version of Microsoft Advanced Threat Analytics. Microsoft ATA collects this information by mirroring authentication network traffic and events to gateway servers, or collecting it directly using agents on domain controllers.
It feeds all of this information to a central server for analysis using machine learning.
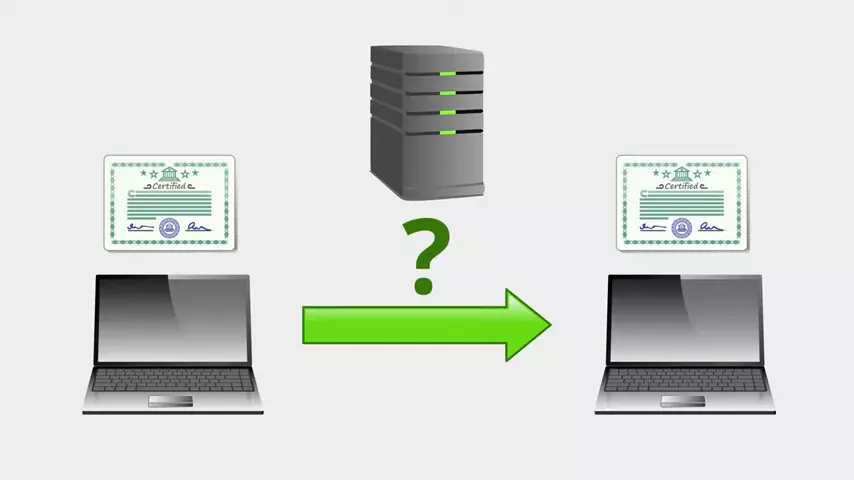
Azure ATP is basically the same thing, but it renames "gateways" to "sensors" and moves the central server up to the cloud. Because it's collecting a ton of authentication traffic from your domain controllers, it can also detect a number of common attacks and reconnaissance activities. Like say someone authenticates on device and receives a ticket proving their identity. Nothing suspicious, right? That's normal. Say someone uses an authentication ticket on another device to access some data. Nothing suspicious there either - that's normal too. Because ATP can combine these pieces of information, though; it could notice that... Hey! That's the same ticket! It was received over here, then used somewhere else. The ticket itself is valid, but how did it get from here to there?
That has all the hallmarks of a successful pass-the-ticket attack having been used to steal a user's network identity.
Another useful thing Azure ATP can do is show lateral movement paths. This basically gives you the roadmap an attacker could follow to gain access to sensitive accounts by hopping from one device to another. Quite often this is how attackers will escalate their privileges - they'll compromise a lower tier of account, and use that to compromise the device that a higher tier of administrator also accesses, and use that device to steal the identity of the higher tier admin. Lateral movement paths can give you visibility of these routes through your environment from one account to the next.
So Microsoft Defender ATP looks at devices, Azure ATP looks at identities... what about Office 365 ATP?
Office 365 ATP (Microsoft Defender for Office 365)
Office 365 ATP focuses on Office 365, or as it's now usually called: Microsoft 365. Office 365 ATP started out life as Exchange Online Advanced Threat Protection. Exchange Online Protection is the fairly basic email filter built into Office 365.
Exchange Online ATP was the upgraded version that provided more advanced protection features; but as Microsoft started to extend some of these features to cover more Office 365 services they renamed it to Office 365 ATP to reflect this. So what does it give you?
The two main features it gives you are sandboxed attachment detonations (what it calls Safe Attachments) and link scanning (what it calls Safe Links). The Safe Attachments feature protects you against as-yet-unknown threats and email attachments. Rather than just relying on signatures of known threats, it takes an attachment and runs in a virtual machine in the cloud. Then it watches to see what happens. If this is a Word document, for example, you wouldn't expect much to happen. It should open in Microsoft Word and that's about all. If, on the other hand, it starts downloading a file from the internet and changing system settings, Office 365 ATP knows it's dodgy and can block it. This is a handy feature, because a lot of malicious attachments these days try to avoid getting blocked by not including malware in the file itself. Rather they will use legitimate features like scripts and macros to attempt to download the malware. after they've been scanned
The Safe Links feature rewrites links in received emails so they go to a Microsoft service instead of the original destination. The service scans the destination of the original link to see if it looks dodgy. When a user clicks a link in their email they're taken to the Microsoft service, which either redirects them back to the original destination or displays block page, depending on what it found when it scanned it. Again, this helps prevent attackers from getting around malware scans by simply linking to the malware instead of including it in the email.
These features aren't just about malware, though. They also integrate anti-phishing capabilities to try and crack down on scam emails that either take you to fake login pages or try to persuade you to transfer money. Phishing is a plague for Office 365 admins, and it's the source of most cloud breaches I've come across. Because it's such a problem, Microsoft have taken some of the previously ATP-exclusive anti-spoofing features, and included them in the standard Exchange Online Protection offering that you get with any plan that includes email. Integration with Safe Links and Safe Attachments, as well as more flexible policies, though; still require ATP.
Whilst these Safe Attachments and Safe Links features started off as features of the Exchange Online email filter; they're now available for use with SharePoint, OneDrive, Teams, and the Office client apps as well. That's why they renamed it from Exchange Online ATP to Office 365 ATP.
Subscription Options
That's the different ATP solutions in a nutshell. How do you actually get hold of them? Microsoft licensing is a bit of a labyrinth, so let me try to help with this; but bear in mind it could change in the future.
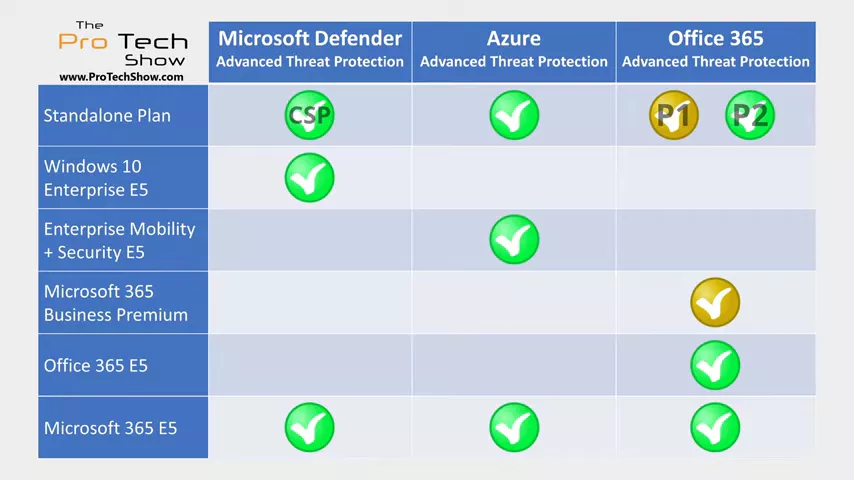
Microsoft Defender ATP is part of the Windows 10 Enterprise E5 subscription; or if you're an education customer the equivalent is Windows 10 Education A5.
Windows 10 Enterprise E5 is included in Microsoft 365 E5, so you get it as part of that as well. Again, for education customers that would be A5. As a general rule, if i say E5 it'll be A5 for you.
Finally, there is a standalone plan, but it's only available from a Cloud Solution Provider. So you'll need to speak to your Microsoft partner about that one. Azure ATP is part of the Enterprise Mobility and Security E5 subscription. Because EM+S E5 is included in the Microsoft 365 E5, you also get it as part of that.
There's also a standalone plan called "Azure Advanced Threat Protection for Users". The "for users" bit is the old name of the product they used when it was in preview, so it's possible those two words might get dropped in the future. Office 365 ATP comes in two standalone flavors: Office 365 ATP Plan 1 contains all of the features I mentioned in this article. Office 365 ATP Plan 2 contains everything in Plan 1, plus additional administrative tools for reporting and investigation, as well as an attack simulator.
All of the features of Plan 2 are included in Office 365 E5; and of course Office 365 E5 is included in Microsoft 365 E5, so you get it in that as well. Microsoft 365 Business Premium does include Office 365 ATP as well, although that one has the features of Plan 1 rather than Plan 2. The easiest solution here is to buy Microsoft 365 E5 and you get all of them; and that's clearly what Microsoft want you to do.
Remember that whilst the larger suites generally represent the best value for what they include, this only counts if you actually use all of the features. Be realistic and buy what you need. I come across a lot of organisations that pay huge amounts of money to have all of the options, and then only use a fraction of them. You can always upgrade later as you grow into the additional services if need be.