Zero-knowledge proofs (ZK proofs) have emerged as a groundbreaking cryptographic technique with the potential to revolutionize privacy, security, and trust in various domains using blockchain development services. In this comprehensive blog, we delve into the fascinating world of ZK proofs, exploring their use cases, applications, and implications across different industries.
Understanding Zero-Knowledge Proofs
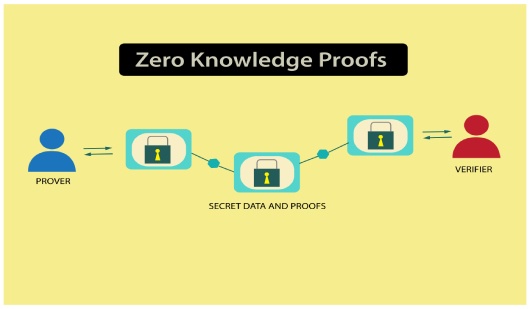
Zero-knowledge proofs are cryptographic protocols that allow one party (the prover) to prove the validity of a statement to another party (the verifier) without revealing any information beyond the statement’s truth. Fundamentally, ZK proofs allow calculations or claims to be verified without revealing the underlying information or inputs.
Also, Read | Exploring zkSync for Optimizing Blockchain Scalability
Key Properties of Zero-Knowledge Proofs:
Privacy
ZK proofs protect sensitive data privacy by enabling communication between parties without disclosing any private information.
Verifiability
ZK proofs ensure trust and integrity in transactions by enabling quick and verifiable authentication of statements or computations.
Efficiency
Because of their computational efficiency, ZK proofs may be quickly verified and scaled to a wide range of applications.
Soundness
ZK proofs provide strong guarantees of correctness and security, ensuring that only valid statements can be proven true.
Use Cases and Applications of ZK Proofs
Privacy-Preserving Identity Verification
One of the key use cases of ZK proofs is to authenticate identities and credentials without disclosing personal information, enabling privacy-preserving identity verification in various contexts such as online authentication, access control, and KYC (Know Your Customer) processes.
Applications
- Decentralized identity platforms
- Secure login systems
- Identity management solutions.
Confidential Transactions
ZK proofs provide financial privacy and secrecy in cryptocurrency transactions by enabling the verification of transaction validity without disclosing the transaction details.
Applications
- Privacy-focused cryptocurrencies
- Confidential payment systems
- Secure financial transactions
Secure Data Sharing and Collaboration
Secure data sharing and collaboration in delicate situations are made possible by ZK proofs, which enable parties to demonstrate the accuracy of computations or data without disclosing the underlying data.
Applications
- Secure multiparty computation
- Confidential data analysis
- Private information sharing among organizations
Supply Chain Traceability and Provenance
ZK proofs can be utilized to prove the authenticity and integrity of supply chain data, enabling transparent and verifiable traceability of goods and products from origin to destination.
Applications
- Supply chain management
- Product authenticity verification
- Anti-counterfeiting measures
Decentralized Finance (DeFi) and Blockchain
ZK proofs offer privacy, scalability, and efficiency solutions in decentralized finance applications, enabling confidential transactions, scalable computations, and secure asset transfers.
Applications
- Privacy-preserving smart contracts
- Confidential asset swaps
- Scalable blockchain solutions
Also, Check | Comprehending ZK Rollups | Layer 2 Scaling Solutions
Conclusion
Zero-knowledge proofs represent a powerful cryptographic tool with diverse applications and far-reaching industry implications. From enhancing privacy and security to enabling scalable and efficient transactions, use cases of ZK proofs offer innovative solutions to complex challenges in today’s digital world. As the technology continues to evolve and mature, we can expect to see increased adoption and integration of ZK proofs in various domains, unlocking new possibilities for privacy-preserving and trustless interactions in the digital age. If you are interested in developing your project using ZK proofs, connect with our blockchain developers for more information.

No comments yet