Kleber Souza, an engineer at Canonical who maintains Linux kernel packages for Ubuntu, has announced a new kernel update cycle. The new cycle, which is codenamed "4/2", involves generating additional SU kernel package updates (Security Update) that include fixes for urgent issues and vulnerabilities flagged as dangerous and critical.
Under the new scheme, SRU (Stable Release Updates) kernel packages will be published every 4 weeks, carrying over fixes from corrective releases of the Linux kernel. Two weeks after the start of the SRU update cycle, an SU update will be published separately to include fixes for only dangerous vulnerabilities and critical issues. SRU updates will take 4 weeks to prepare and test before publication, while SU updates will take 2 weeks. In the remaining two weeks before the end of the overall SRU cycle, fixes for dangerous vulnerabilities and important issues will be moved to the upcoming SRU update.
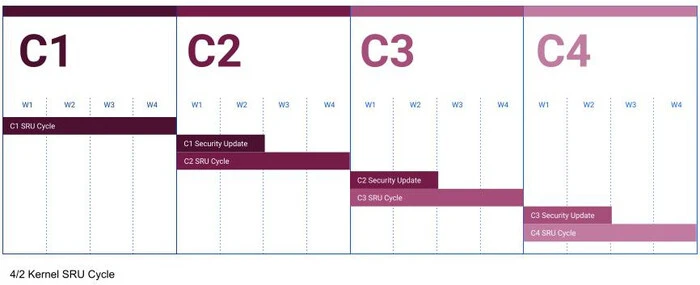
Thus, new versions of kernel packages will now be published every two weeks, and the maximum delay in fixing dangerous vulnerabilities will not exceed two weeks. For example, packages with kernel 6.2 for Ubuntu 23.04 will be formed in the following order: in the week beginning August 7, will be published SRU-update with the transfer of fixes from the main branch of the kernel, August 21 will be formed SU-update with vulnerability fixes, September 4 - SRU-update, September 18 - SU-update, etc.
The new scheme is expected to speed up the delivery of vulnerability patches to users and increase the predictability of the development process. Under the old scheme, which used a three-week development cycle, there were problems with the timeliness of vulnerability fixes. If the schedule was followed, users had to wait up to three weeks for non-critical vulnerabilities to be patched. If critical issues, vulnerabilities or regressions were discovered, unscheduled updates were generated, which disrupted the process of preparing the next scheduled kernel update. As a result, unscheduled updates shifted the cycle of scheduled update generation and delayed its publication. Correspondingly, the delivery of patches for non-critical vulnerabilities was also delayed.

No comments yet