Two components of the Linux kernel contain security vulnerabilities that grant local attackers root shell access. A first exploit has been made public.
Two components of the Linux kernel are affected by security vulnerabilities that allow local attackers to elevate their privileges. A Use-After-Free vulnerability in the nf_tables module as well as a logic error in FUSE allow unprivileged users to take over the target system with root privileges.
FUSE (Filesystem in Userspace) is used to mount non-Linux filesystems such as NTFS or UDF (DVDs) without requiring the user to have additional privileges (such as root access). Security researchers have now found a way to disrupt the interaction between the Linux kernel and FUSE while copying files, thus gaining root privileges. The security vulnerability affects systems with kernel versions between 5.11 and 5.19, as well as installed FUSE.
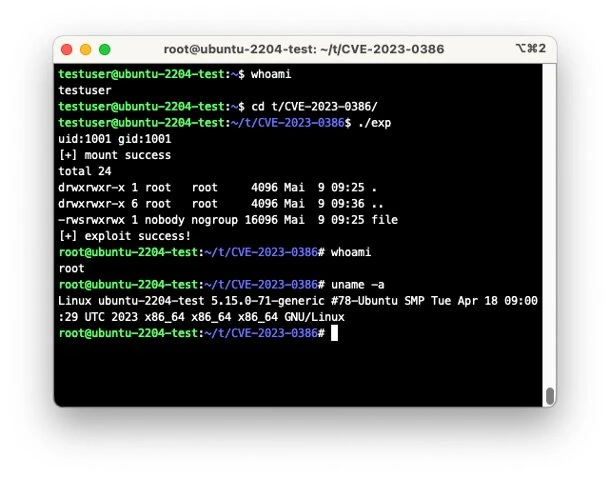
A Chinese security researcher using the pseudonym "breeze chenaotian" has published a detailed analysis of the bug and explains that the vulnerable function called kuid_has_mapping makes incorrect user rights assignments in the different namespaces of the Linux kernel under certain conditions. During a test on a freshly installed Ubuntu VM (22.04), heise Security was able to successfully reproduce this FUSE vulnerability using the proof-of-concept exploit. The security vulnerability is listed with the identifier CVE-2023-0386 in the relevant databases and is prioritized as "high" with a CVSS score of 7.8.
In addition to all Linux systems with vulnerable kernel versions 5.11 to 5.19, a number of Netapp products and probably also Linux-based appliances from other manufacturers are affected. Updated kernel packages for most Linux distributions are still pending, but Ubuntu has already responded by releasing a new kernel.
PoC still under embargo
Relatively little is known about the security vulnerability with ID CVE-2023-32233 in nf_tables. A group of Polish security researchers has published the bug on the oss-sec mailing list and claims to have developed a root exploit for it. However, this will only be published on May 15th - until then, an embargo period applies that is intended to give Linux developers and distributions an opportunity to secure their systems. When manipulating the nf_tables configuration, directly consecutive operations are processed incorrectly under certain circumstances, leading to a faulty memory access (use after free). Again, remote attacks are not possible - attackers therefore need access to a user account on the target system.
According to the discoverers, various current Linux kernel versions are affected, including the current stable kernel 6.3.1. The bug was fixed on May 2nd by a kernel patch, but the major Linux distributions have not yet released updated kernel packages.


Comments (1)